The Cobbler’s Children Get New Shoes
 Our business website looked great when it went live in 2002. It was modern, clean, quick-to-load, and full-featured. We did updates and edits throughout the years, but the basic layout and functionality was rooted in standards and technology of the early new century.
Our business website looked great when it went live in 2002. It was modern, clean, quick-to-load, and full-featured. We did updates and edits throughout the years, but the basic layout and functionality was rooted in standards and technology of the early new century.
The original home page is shown on the right (and click on the picture to go to the actual old site).
But, we’re not in 2002 anymore. It was way past time to create an updated Ozdachs.biz, and we were happy to go live with a new look in early July.
Here are 4 major changes we made… and ones you should consider doing, if your site is 16, 10, or even 6 years old!
Responsive Design
Responsive design means that your site responds (displays) differently depending upon the layout and size of the user’s screen. Graphics will change size and columns will break differently depending on what type of device your visitor is using. Your pages will look different on desktops, tablets, and cell phones.
For some industries, over half of all website visitors are using their cellphones, so making pages that look look and work well on small screens is important.
Responsive design lets your web pages display on the phone without making the user scroll or manually resize the screen. Users like responsive sites a lot. They don’t like to have to scroll left and right to see what’s there.
- Moreover, Google ranks sites that are NOT responsive lower in search results. If you’re hoping that new visitors will discover your site when they look up your keywords on Google, you need to have a responsive site.
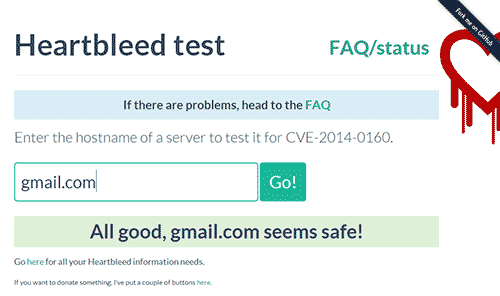
Want to see if your current site is responsive?
And then see if the small formats are user-friendly: Use Google’s free testing tool.
Larger and More Complex Graphics
Fifteen years ago web designers had to worry about the size of photographs and functional code on their site because download speeds were low. Remember the hot technology of DSL? The top DSL speed was 128 kilobits per second to 3 Megabits per second (Mbps). Big pictures, maybe 8 Megabits in size, could make your website take forever to display.
Most people now get 10, 20, 100, or even 1000 Mbs from their Internet Servic Provider!
Users and search engines still care about speed, and Google boosts your site in search results if it loads in a reasonable amount of time. But, with speeds 100 faster than they were a few years ago, images can be larger and you can do some fancy displays with pictures and text.
You want larger photos and more interesting graphics — properly focused, they grab the attention of your visitors.
WordPress for Code Management
Initially all of Ozdachs’ sites were simple HTML sites with maybe some JavaScript written for navigation or simple image swapping. To publish a site or to make changes, you had to have a What You See Is What You Get (WYSIWYG) HTML authoring tool like FrontPage or Dreamweaver on your computer. You’d make your changes locally and then upload the HTML code to your hosting service.
Now, up to 30% of website are developed using the open source code management system WordPress. WordPress is constantly being updated and improved. Third parties are writing tons of plug-in applications to increase the functionality of WordPress sites. In addition, scads of developers have created templates that sit on top of WordPress and let you apply and extensively customize prefabricated websites and web pages.
WordPress sites live on the hosting service, not on any one person’s computer. With proper security, your developer or you can update your site content from anywhere with an Internet connection. You do your edits using a web browser. You go to your site, enter in your authoring credentials, and make your changes. There is no special software required on your computer.
WordPress originally was known for supporting blogs like this one. But, now entire sites are built on WordPress.
Ozdachs uses WordPress —and currently the Avada template — for most of its clients. The choices of looks and features which can be selected is rich. Our web design home page shows a selection of client sites, and all but one of them are WordPress sites using Avada.
Frankly, we couldn’t offer the range of looks and functions to our clients without relying on whiz-bang products from third parties. Developers and companies are producing more reasonably-priced tools for the WordPress platform than for any other offering. So, we are WordPress fans.
HTTPS Protocol
When your old site was created, chances are your hosting service only delivered pages to visitors using Hypertext Transport Protocol, and the site’s address in web browsers showed up as “http://www.yoursite.com”.
The standard now for websites is now Hypertext Transport Protocol Secure or HTTPS. This means that your website’s connections with your visitors are encrypted and that your site has been verified as real by a third-party issuer of security certificates. Check out this discussion of what HTTPS is and why you want it.
Most of Ozdachs clients collect no sensitive data from their visitors. Getting a security certificate and delivering content by HTTPS might seem like overkill.
However, Google threatens to penalize all sites that are not HTTPS by displaying them lower in search engine results. And, also, some of your users will be reassured by seeing the padlock icon and a “Secure” indication in the browser’s address field when they use your site.
We decided to pay for a upgraded SSL certificate for our business site so visitors know we know the technology and understand that we can be trusted.
Check Out Our New Shoes
That’s it! Our four big changes:
-
- Responsive Design
- Larger and Complex Graphics
- WordPress Base
- HTTPS protocol
The leap from a 2002 look and a 2018 website is a big one.
We like the fancy look look of our new shoes.
Check out Ozdachs’ Internet Consulting business site, and let us know what you think and if you have any questions on what we’ve done.